How Pegasus Spyware can control your mobile?
Pegasus is a type of software designed for mobile phones, and it has the capability to turn an installed mobile phone into a mobile surveillance device. This capability is under the control of the hacker who has gained access to the phone.
International investigators categorize this as a mobile application used for surveillance of journalists. They believe it is primarily employed for monitoring the information sources of media professionals.
Information has been received indicating that this surveillance application was used in 45 countries in 2018 alone. Among these countries are Mexico, Saudi Arabia, Bahrain, Morocco, Israel, the United States, and the United Arab Emirates.
Investigators have confirmed that this application has been used to monitor journalists and civil activists in these countries.
According to Citizen Lab, in 2019, the widely used WhatsApp application was targeted by Pegasus surveillance, affecting approximately 100 human rights activists and journalists across about 20 countries worldwide.
Facebook, the owner of the WhatsApp application, later revealed that the threat was from Pegasus, a surveillance software developed by the Israeli NSO Group. This software could potentially be used by state security services to gather information on criminals and terrorists, or could be related to other similar applications.
These spyware applications have the capability to monitor, record, and collect both existing data on an infected phone and future activities. This includes obtaining information on phone conversations (call and call logs), messages exchanged through messaging apps, and real-time location data of the mobile phone.
Not only that, but the Pegasus surveillance software also has the capability to activate the camera and microphone of the relevant mobile phone, allowing for the observation of surrounding events and eavesdropping on conversations.
The Pegasus spyware can operate undetected on mobile phones with Android, iOS, and BlackBerry operating systems, meaning that the owner may not be aware of its presence. Identifying its activity on a device generally requires the assistance of a security expert knowledgeable in system security.
If you believe that you or someone you know might be targeted by surveillance or that the Pegasus application is currently active on your phone:
- Immediately stop using the phone.
- Keep the phone in a secure and isolated location where neither you nor your trusted contacts are present.
- Log out of all user accounts associated with that phone.
- Change all passwords on any computer or other devices.
- If you are not well-versed in technical matters, seek assistance from a digital security expert. There are several ways in which the Pegasus application could be installed on your phone.
1. Zero-day attacks
Through this method, there is a possibility of installing the application on your phone via a vulnerable spot in an app that is not properly updated, without the user’s intervention.
For example, in the case of the WhatsApp installation mentioned earlier, the person owning the phone received a WhatsApp call from an unknown number. As a result, the WhatsApp app crashed, and there may have been a missed call or a number that did not appear in the call registry.
Mitigating the impact of zero-day attacks is not a simple task. In other countries, journalists targeted by this threat have become accustomed to buying inexpensive, small mobile phones regularly, using them for a short period like a month, and then destroying them before switching to a new device.al security in an increasingly surveilled world.
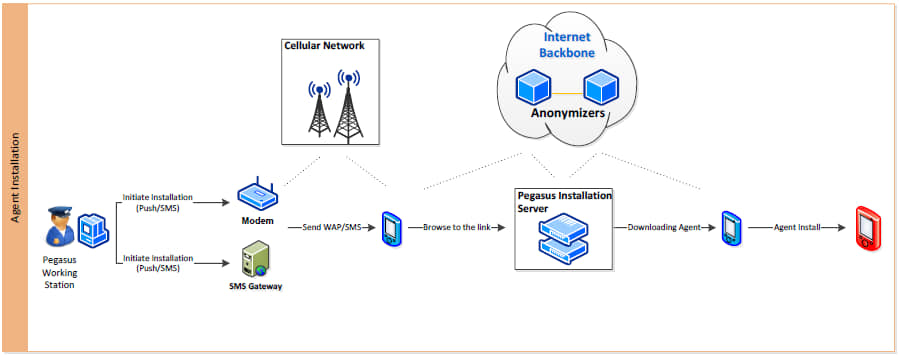
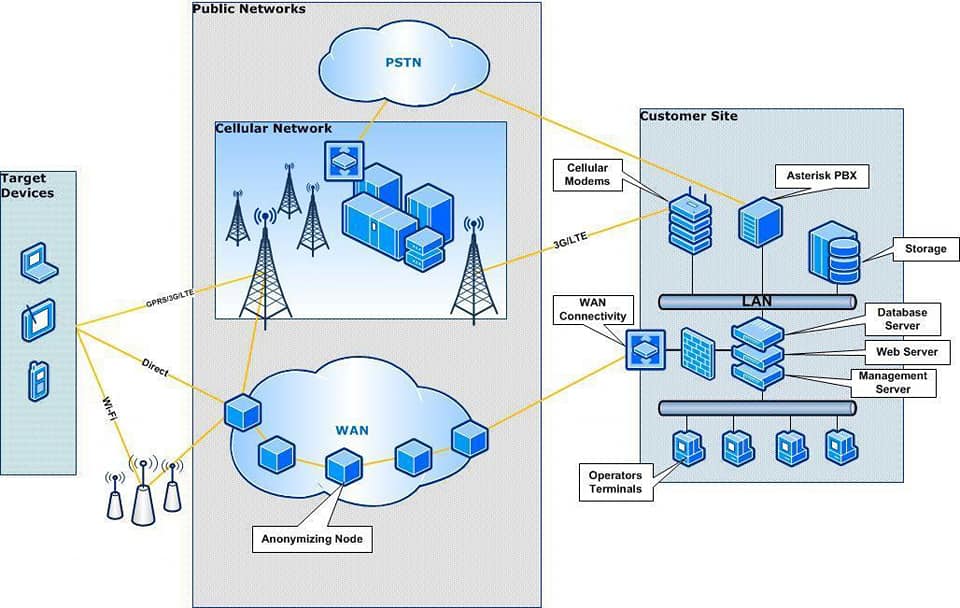
2. Spear-phishing attacks
Through this method, hackers send a message designed as needed to a target journalist or user. This message often contains a link or document that appears essential, creating psychological pressure on the user to click on it.
This message can arrive as a text message (SMS), email, chat messenger message, or social media message. Once the target user clicks on the link, the Pegasus application is installed on their phone.
2.1 According to investigations conducted by Citizen Lab and Amnesty International, the aforementioned messages can reach you in the following ways:
- As a message received through a consulate office you know or a media organization you are familiar with.
- As a message indicating that the target user’s phone is currently under security threat.
- As a message related to your employment.
- As a message containing photos of or information about close, trusted individuals.
- As a message related to financial services provided by credit card, bank, or other institutions.
2.2 To protect yourself from such spear-phishing attacks:
- A. Verify the sender of the message through other means if possible. If the sender is someone you do not know, checking the information through secondary sources might not be entirely safe, as that information could be deliberately crafted by the hackers to mislead.
- B. If you must open a message, do so using a secondary device. Keep this secondary device deactivated and with its battery removed whenever not in use. Regularly perform a factory reset on this device, as it too might be compromised.
- C. If the message contains a shortened link (e.g., using URL shorteners like Bitly or TinyURL), use a URL expander like Urlex to check if the link is safe.
- D. Avoid using the default web browser and instead use an alternative browser. For example, since Android devices commonly use Google Chrome and Apple devices use Safari as default browsers, Pegasus spyware is often designed to target these default browsers. Using an alternative web
- browser can reduce the risk of exposure.
3. Physical installation by an adversary
There is also the possibility of physically installing surveillance or information-gathering software on the target individual’s phone.
- A. Do not leave your mobile phone unattended in places where others can access it.
- B. If your phone is handed over to someone else for inspection during security checks, such as at border crossings or during searches, ensure that it is deactivated and handed over. Otherwise, remain vigilant about your phone at all times.
- C. Use passwords that are difficult for others to guess, incorporating a combination of letters, numbers, and symbols.
Author

Dinesh Abeywickrama Ph.D. (Reading), MBCS, MBA, BCS
References
- Chawla, A. (2021). Pegasus Spyware – “A Privacy Killer.” SSRN Electronic Journal. https://doi.org/10.2139/ssrn.3890657
- Rudie, J., Katz, Z., Kuhbander, S., & Bhunia, S. (2021). Technical Analysis of the NSO Group’s Pegasus Spyware. 2021 International Conference on Computational Science and Computational Intelligence (CSCI), Las Vegas, NV, USA, 747-752. doi: 10.1109/CSCI54926.2021.00188
- Citizen Lab. (2018). Hide and seek: Tracking NSO Group’s Pegasus spyware to operations in 45 countries. University of Toronto. https://citizenlab.ca/2018/09/hide-and-seek-tracking-nsogroups-pegasus-spyware-to-operations-in-45-countries/
- Amnesty International. (2021). Forensic methodology report: How to catch NSO Group’s Pegasus.
- Amnesty International Security Lab.
- https://www.amnesty.org/en/latest/research/2021/07/forensic-methodology-report-how-to-catchnso-groups-pegasus/
- NSO Group. (2021). Transparency and responsibility report. NSO Group Technologies. https://www.nsogroup.com/
- Abeywickrama, D. (2021, April 10; rev. 2024, September 19). Pegasus that secretly monitors your mobile phone. Siyalla. https://www.siyalla.com/pegasus-spyware/